Where Data Security Meets Human Context
Lightbeam links every piece of sensitive data to the person it belongs to, enabling precise discovery, governance, and remediation while automating compliance across your entire data estate.
Identity-Centric Data Protection
Map every data point to its owner for precise classification, risk detection, and remediation.
Automated Risk Remediation
Detect and fix overexposed data or risky access instantly to reduce breach risk.
Compliance Without the Burden
Automate reporting, DSRs, and retention to meet global regulations at scale.

90%
Reduction in manual data security and privacy operations
75%
Faster remediation of risky data access
80%
Less time needed to prepare audit reports
Many Problems Solved. One Powerful Platform
Lightbeam integrates eight powerful capabilities to protect sensitive data, reduce risk, and automate compliance at scale.
Data Security Posture Management (DSPM)
Continuously monitor and improve your security posture to prevent breaches before they happen.
Learn MoreData Classification
Classify data by identity, content, and context with AI for unmatched accuracy and precision.
Learn MoreRisk Scoring
Prioritize threats with context-aware scoring so teams fix the riskiest issues first.
Learn MoreAutomated Remediation
Resolve security and privacy risks instantly with policy-driven automation.
Learn MorePrivacy at Scale
Meet global privacy obligations with workflows that slash manual effort by up to 90%.
Learn MoreAccess Governance
See and control who can access sensitive data, enforcing least privilege automatically.
Learn MoreRansomware Protection
Detect and contain ransomware threats early to protect critical data and operations.
Learn MoreUser Entity Behavior Analytics (UEBA)
Spot insider threats and suspicious activity by understanding normal user and entity behavior patterns.
Learn MoreLightbeam Data Identity Graph: The Power of Human Context
Connect Data and People
Map every file or record to the person or entity it describes for unmatched accuracy.
Intelligent Access Governance
Track and analyze access paths for all human and service accounts in real time.
Contextual Risk Analysis
Combine data, identity, and access history to detect and fix high-risk exposures.

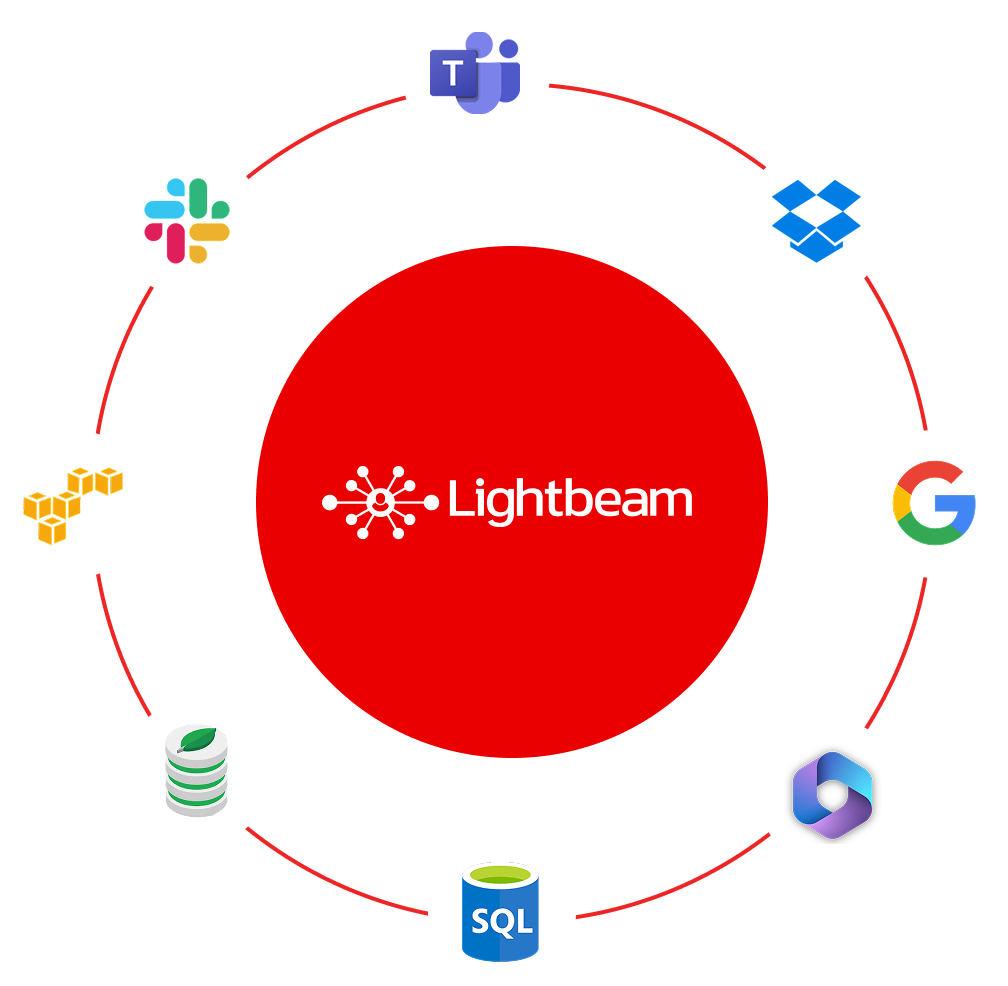
Connect to Any Data Source
Lightbeam supports API-based integrations with hundreds of structured, unstructured, and semi-structured data sources, ensuring complete coverage across your data estate.

"They have been very helpful with getting everything set up and have gone above and beyond to meet the needs of our organization and security posture. They continue to make changes and improvements based on feedback."
Manager, Legal and Compliance
Education